Information Security Policy
Information Security Certification
Information Security Governance and Strategies
Xintec has established Proprietary Information
Protection Committee (PIP Committee) since January, 2008 to protect
company and customer’s confidential information. PIP Committee is
responsible for managing and supervising the control of confidential
information, and also they enact “Confidential Information Protection
Policy” and “Confidential Information Protection Management Regulation”
which clearly list management policies, procedures, and specifications
of confidential information protection. Xintec’s Information security
objective is to build a complete information security system and
comprehensive security defensive ability to ensure information security.
Identify risks, prevent and improve weakness through various security
technologies. Make employees have correct concept and awareness on
information protection, and reduce the risks from information leakage
and cyber-attacks. Maintain company’s competitive advantages.
In line with cyber security trends and to establish a
standard operating procedure for cyber security across company, ensuring immediate
and resilient response to threats, our company obtained ISO 27001 Information Security
Management System certification in September 2025. The certificate is valid from
September 3, 2025 to September 2, 2028.
5 main goals; fulfill PDCA Cycle:
1. Build and fulfill confidential information and
information security management system.
2. Comply with requests from the laws and contractual
obligations related to information security.
3. Indeed give education and propaganda about
confidential information protection and information security to
employees and related groups.
4. Assess and identify risks. Set a goal for improving
and control measures.
5.Improve information security management system
through internal audit.
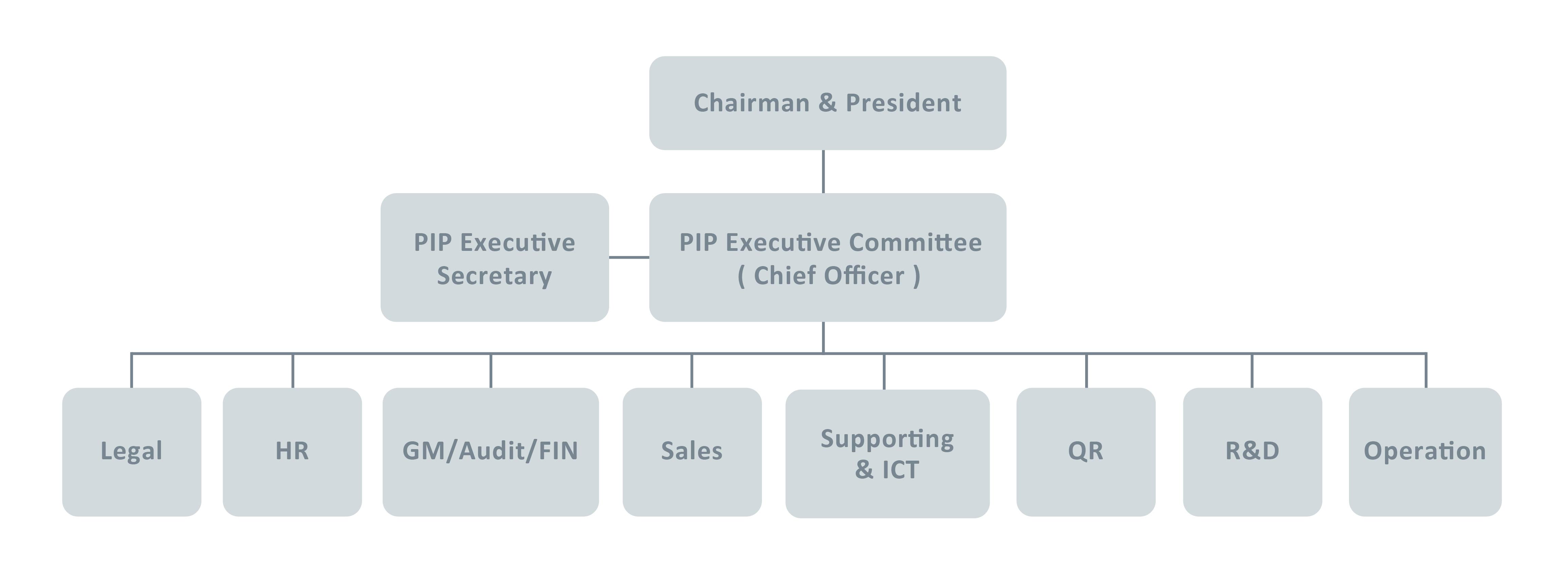
Information Security Organizations
PIP Committee’s duty is to manage, plan, supervise, and
promote departments for information security. PIP Committee and IT
department would together build a complete system and comprehensive
defensive ability. Meetings would be held seasonally by the Committee
members to check information security policy and its result. Annually,
PIP Committee would make report to the board, letting the board
understand situations of implementing information security.
1.PIP Committee: It is composed of representatives
assigned by each department head. Duty: Discuss, establish, audit, and
promote confidential information security controls.
2.PIP Executive Department: Plan, supervise, and promote
confidential information security controls
3.IT: Build and manage information security system.
Assist in evaluating, setting up and managing software and hardware
based on PIP Committee’s decision and requirement. Conduct abnormal data
of communication and information storage analysis. If there is any
abnormality, notify PIP Committee.
Risks Management and Resources
1.Obtain ISO 27001 certification and establish standardized processes.
2.Asset Inventory and Risk Assessment: Regularly conduct identification and implement sensitive information classification and grading (inventory, labeling, and grading) to ensure precise control.
3.Supply Chain Security Management: Incorporate cyber security questionnaires and on-site visits to key suppliers to extend defense depth to partners.
4.Strengthen firewalls and other equipment to prevent zero-day attacks and block phishing emails.
5.Implement web browsing isolation to ensure employee online security.
6.Mail Review and DLP System Control to prevent data leakage of confidential information.
7.Make emergency response plan and drill. Clearly enact Recovery Time Objective (RTO) and Recovery Point Objective (RPO) of the main business. Settle proper backup system and backup plan.
8.Social Engineering – Adding suspicious email recognition mechanism, Phishing email, drill and cases propaganda.
9.Regularly hold propaganda and conduct audit to check the implementation of confidential information protection.
10.Strengthen information security defense, evaluate and improve the weaknesses of external services through the third-party security risk management platform.
11.Regularly hold hazard identification, risk assessment, and improvement operation.
12.Strengthen server protection, management and abnormal movement mechanism.
13.Set up a Security Operation Center (SOC) to control real-time information security status, focus on relative events, manage the rising alarm, and become the command center when any issue happens.
14.Establish SIEM (Security Information and Event Management), concentrate records collected by each system, integrate event alarms, correlation analysis, output data reports to assist security personnel in establishing overall environmental visualization more efficiently and promptly troubleshoot problems.
2025 Training and Audit
1.Total 12 PIP management meetings and 4 PIP Committee meetings.
2.All employees in company completed PIP training and audit.
3.Information security personnel have completed total 35 training sessions.
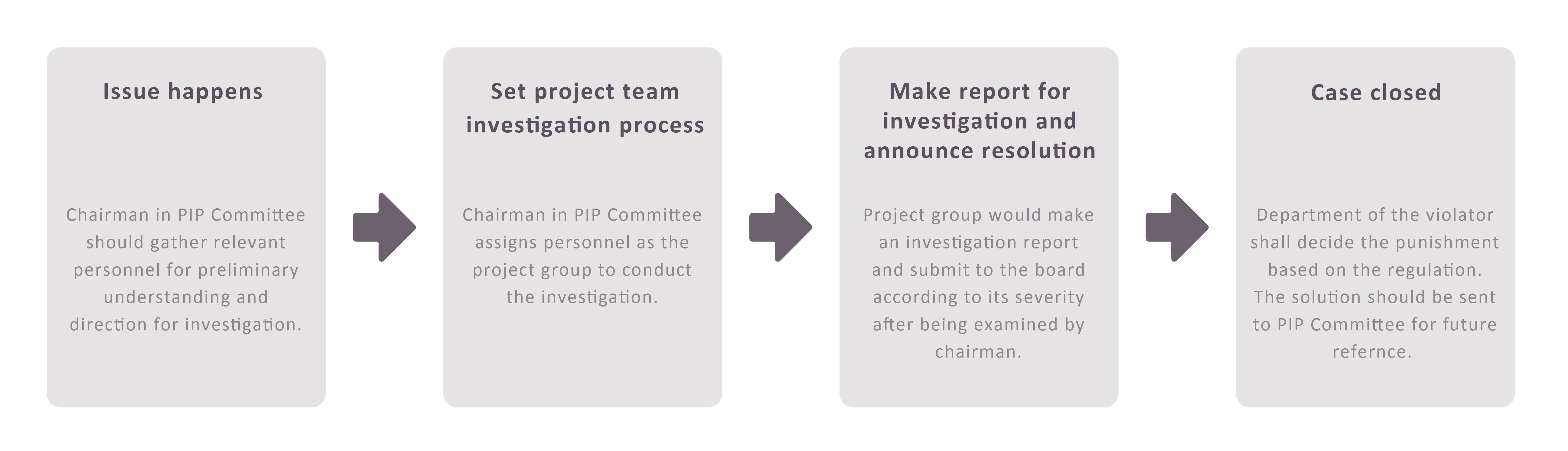
Information Security Issues
Flow for investigation:
Company didn’t get loss from serious information
security issue in 2025.
.png)